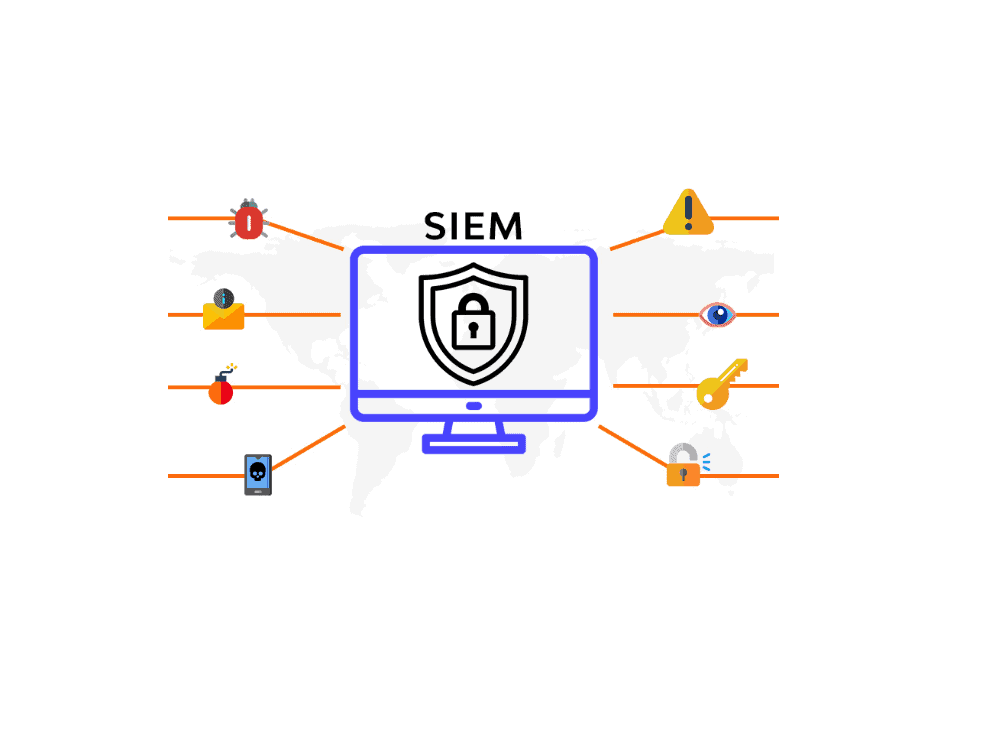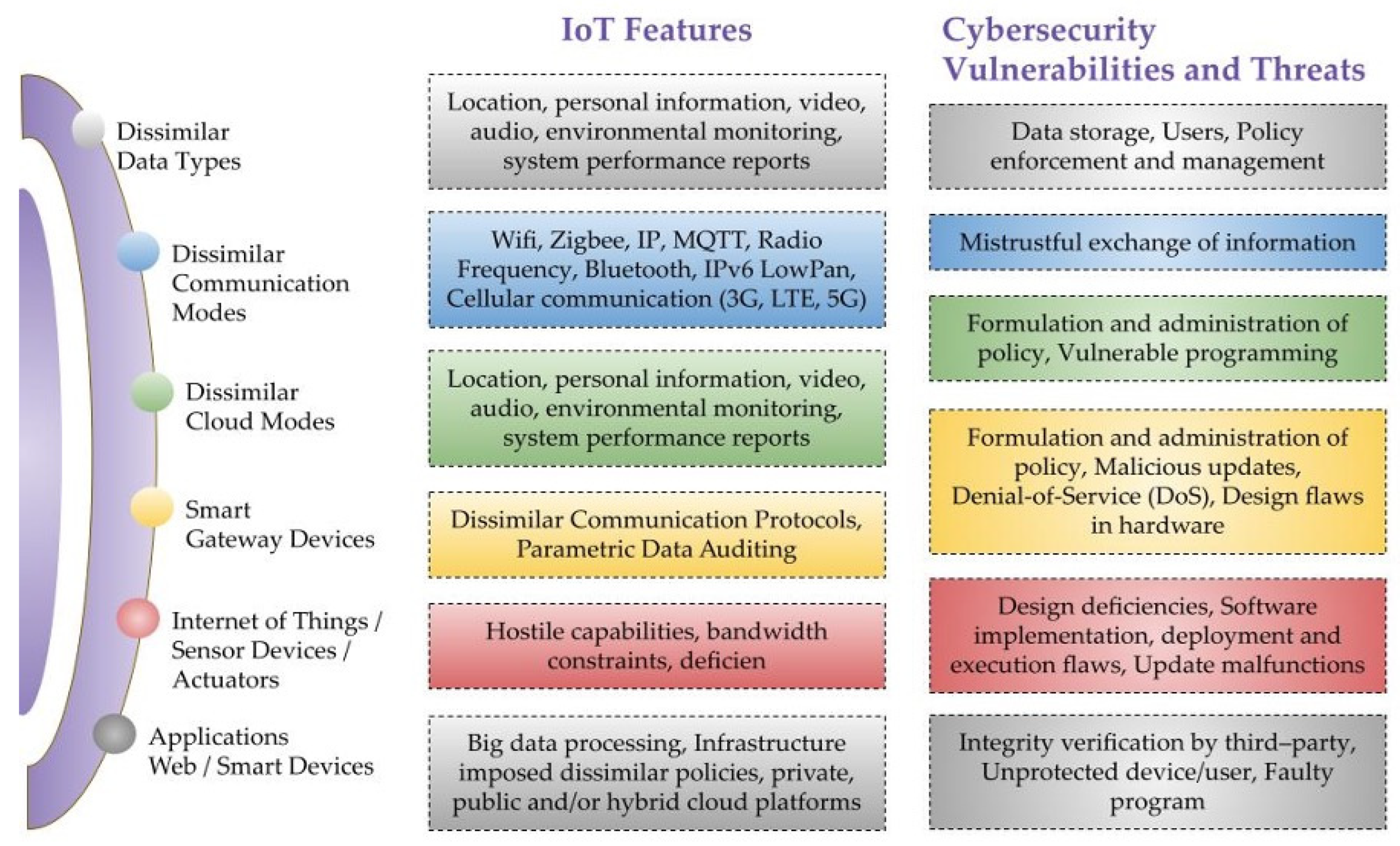
Sensors | Free Full-Text | A Critical Cybersecurity Analysis and Future Research Directions for the Internet of Things: A Comprehensive Review
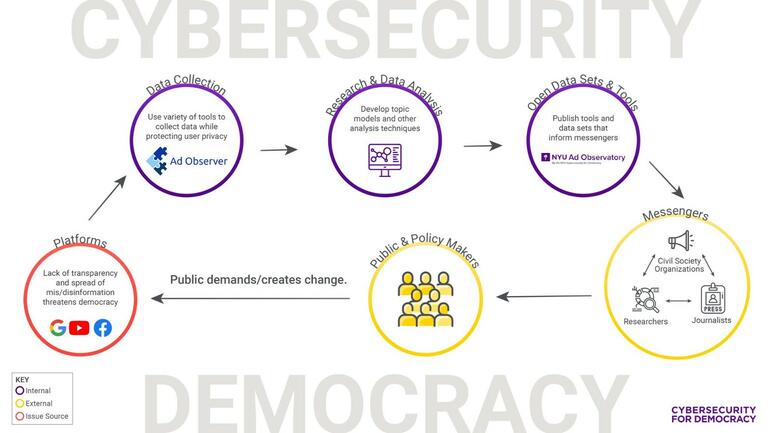
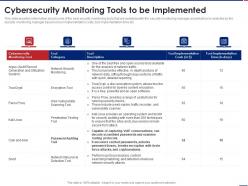
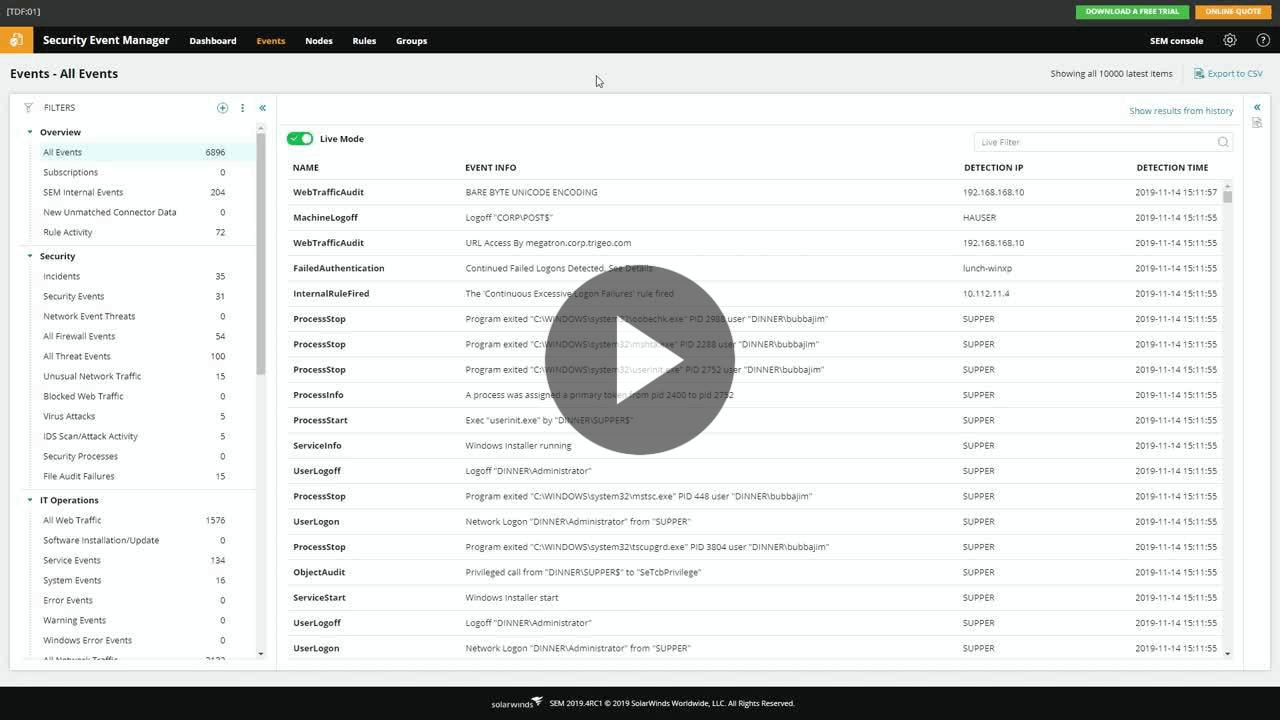
Cybersecurity for Democracy / Monitoring tools / Tools / Media Freedom in Europe - Resource Centre by OBCT - Resource Centre